What Is MPLS? Multiprotocol Label Switching Overview
Understanding MPLS helps businesses build reliable, high-performance connectivity across wide area networks. Multiprotocol Label Switching (MPLS) directs traffic through predefined network paths to improve speed, stability, and efficiency for voice, video, and critical applications. In this article, Axclusive ISP explains how MPLS works and its role in modern enterprise networking.
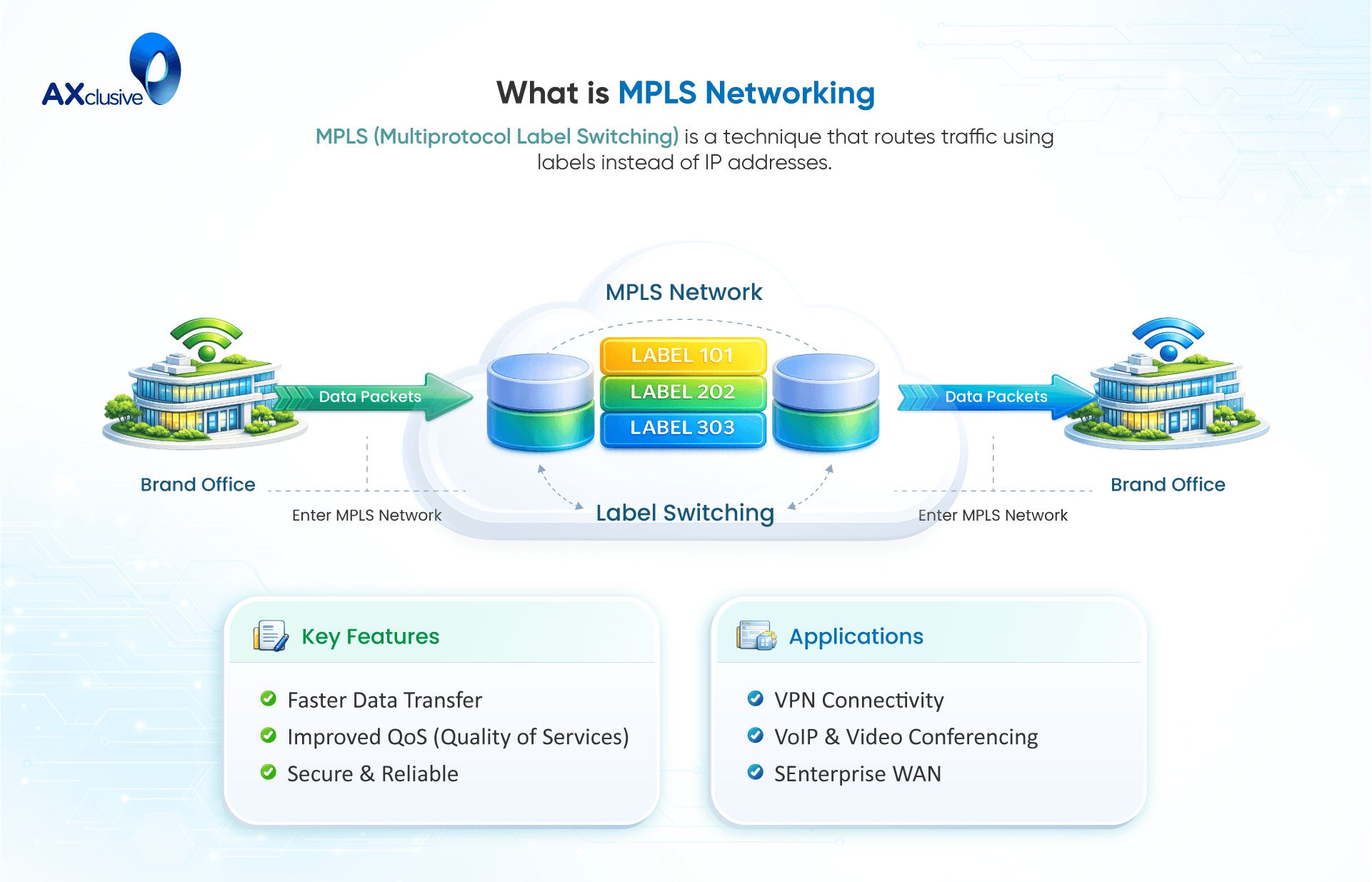
What Is MPLS?
Multiprotocol Label Switching (MPLS) is a highly efficient data forwarding technology designed to regulate, secure, and accelerate traffic across enterprise Wide Area Networks (WANs). Unlike traditional IP routing, where every individual router must independently inspect a packet and calculate its next hop, MPLS assigns specific labels to data packets the moment they enter the network. These labels direct traffic along predetermined, optimized routes rather than forcing packets to navigate intermediate destinations. By establishing these dedicated network "expressways," MPLS eliminates redundant routing decisions, ensuring reduced latency, consistent performance, and reliable connectivity between geographically dispersed branch locations.
Want to learn how modern data centers and cloud networks achieve scalable Layer 2 connectivity? Explore our guide on What Is VXLAN to understand how VXLAN supports network virtualization, segmentation, and large-scale infrastructure deployment.
How does routing work in MPLS?
MPLS fundamentally changes how data traverses a network by replacing complex IP routing lookups with a highly efficient, label-based forwarding mechanism. It is protocol-agnostic, meaning it can encapsulate and transport various types of traffic (such as Ethernet, DSL, or ATM) over the same infrastructure.
The core operational process of MPLS occurs in three distinct phases:
- Ingress (Classification and Labeling): When a data packet first enters the MPLS network through a Label Edge Router (LER), it is analyzed and assigned to a Forwarding Equivalence Class (FEC) based on its destination and traffic type. The router then appends a short bit-sequence label to the packet header.
- Transit (Label Switching): This label dictates the packet's exact route, known as a Label Switched Path (LSP). As the packet travels through core routers (Label Switching Routers or LSRs), these devices do not inspect the complex IP address. Instead, they quickly read the label, swap it with the appropriate label for the next hop using a simple forwarding table, and send it on its way.
- Egress (Decapsulation): Once the packet reaches the final edge router of the MPLS network, the label is stripped off. The packet is then delivered to its final destination using standard IP routing.
When MPLS Is Appropriate
Historically, enterprise organizations have deployed MPLS to architect robust, private Wide Area Networks (WANs). It is predominantly used to establish reliable, high-performance connections between a central corporate data center (or headquarters) and geographically dispersed branch offices, manufacturing facilities, or campus networks. Because MPLS guarantees packet delivery and prioritizes traffic, it remains highly effective for latency-sensitive, mission-critical internal applications, such as VoIP communications and real-time database syncing within a traditional "hub-and-spoke" network topology.
While MPLS delivers exceptional reliability, its rigid architecture struggles to support the dynamic demands of modern, cloud-first business models. Organizations are increasingly moving away from pure MPLS networks due to three core limitations: high operational costs, slow circuit provisioning times, and the latency introduced by "backhauling" (forcing cloud-bound traffic from branches to route through the central data center before reaching the internet).
To modernize their infrastructure for remote work, SaaS adoption, and edge computing, enterprises are transitioning to:
- SD-WAN (Software-Defined WAN): A more agile, cost-effective overlay technology that dynamically steers traffic across various transport links (including standard internet broadband and 5G), reducing reliance on expensive MPLS circuits.
- SASE (Secure Access Service Edge): A cloud-native architectural model that converges SD-WAN networking with comprehensive, built-in security protocols (like Zero Trust), optimizing access for a highly distributed, hybrid workforce.
MPLS advantages and disadvantages
| Advantages (Pros) | Disadvantages (Cons) |
|---|---|
| Protocol Agnosticism: Seamlessly encapsulates and transports diverse traffic types (IP, Ethernet, Frame Relay, ATM) over a unified infrastructure. | Premium Cost & Rigidity: Bandwidth is highly expensive compared to broadband. Provisioning physical circuits requires extensive lead times. |
| Advanced QoS: Enforces strict traffic prioritization, ensuring latency-sensitive applications like VoIP and live video operate without packet loss or jitter. | Cloud Incompatibility: Structurally designed for static, point-to-point connections; ill-equipped to handle dynamic, direct-to-cloud SaaS traffic. |
| Mission-Critical Reliability: Utilizes dedicated, engineered paths to provide high stability and competitive Service Level Agreements (SLAs). | Edge Inflexibility: Cannot seamlessly extend to remote workers, mobile users, or temporary edge locations due to its reliance on physical hardware. |
| Bandwidth Guarantees: Allows network engineers to definitively allocate and reserve specific percentages of bandwidth for critical enterprise data. | Lack of Central Management: Lacks the agile, centralized, software-defined management planes found in modern alternatives like SD-WAN. |
MPLS Connectivity Alternatives
MPLS alternatives are networking options that replace or complement MPLS to reduce cost and increase flexibility. They are commonly used to support cloud access, remote users, and modern application traffic.
MPLS vs. Internet Connectivity
MPLS and public Internet connectivity are both widely used options for enterprise networks, but they are designed to meet different operational requirements. While the Internet offers flexibility and lower cost, MPLS focuses on controlled performance and predictable service delivery. Below is a clear comparison that highlights the key differences between the two approaches.
Internet connectivity relies on multiple carriers, public routing paths, and upstream IP transit agreements, where traffic control is not centralized like a private MPLS backbone.
Traffic prioritization: MPLS networks support traffic classification and prioritization, ensuring critical data receives guaranteed handling. Internet connections treat most traffic equally, with no native quality-of-service guarantees.
Support for voice and video: MPLS is commonly used for voice and video workloads because it provides consistent latency and packet delivery. Internet-based connectivity may experience jitter and packet loss, which can affect real-time communication quality.
Service-level agreements (SLAs): MPLS includes defined SLAs covering uptime, latency, and packet loss. Internet SLAs are generally less strict and vary by provider and service type.
Cost structure: MPLS connectivity comes at a higher cost due to managed performance and guaranteed service levels. Internet connectivity is typically more affordable and easier to scale.
Security model: MPLS operates over private networks that are isolated from public traffic, reducing exposure. Internet connectivity uses public infrastructure and requires additional security controls to protect data in transit.
MPLS vs. VPN
MPLS and virtual private networks (VPNs) are both used to connect users and sites securely, but they are built on different network models and serve different operational goals. MPLS focuses on controlled routing and performance, while VPNs emphasize encryption and secure access over public networks. The key differences are outlined below.
Network foundation: MPLS operates over a service provider’s private backbone with managed routing paths. VPNs run on top of the public internet and create a secure tunnel between endpoints.
Performance and speed: VPN connections can use high-speed internet links at a lower cost, making them suitable for high-throughput use cases. However, performance depends on internet conditions. MPLS delivers more consistent latency and reliability due to controlled routing.
Security approach: MPLS networks are logically isolated and use private routing, but encryption is not enabled by default. VPNs are designed around security and always use authentication and encryption to protect data over untrusted networks.
Encryption and authentication: VPNs rely on established cryptographic methods and tunneling protocols to ensure confidentiality and data integrity. Even if traffic is intercepted, encrypted data remains unreadable. MPLS typically requires additional security layers to achieve the same level of protection.
Data protection model: VPNs protect data through encrypted tunnels and user authentication, making unauthorized access difficult. MPLS relies on network isolation rather than encryption for data protection.
Cost and deployment: VPN solutions are generally more cost-effective and easier to deploy, as they do not require dedicated infrastructure. MPLS involves higher costs due to provider-managed circuits and infrastructure commitments.
MPLS vs. IPsec
MPLS and IPsec address different aspects of enterprise connectivity. MPLS is designed to provide controlled routing and predictable performance over private networks, while IPsec focuses on securing data transmission across public networks through encryption and authentication. The main distinctions between the two are outlined below.
Core purpose: MPLS delivers private, provider-managed connectivity with predefined routing paths. IPsec is a security framework that protects IP traffic and is commonly used to build VPN tunnels over the public internet.
Encryption model: MPLS does not apply encryption by default because traffic remains within a private carrier network. IPsec encrypts every packet and verifies its source, ensuring confidentiality and data integrity during transmission.
Cost considerations: MPLS requires dedicated infrastructure and service provider contracts, which increases overall cost. IPsec requires tunnel creation between network endpoints, increasing processing load on security devices and operational effort as the network grows.
Security exposure: MPLS relies on network isolation for protection. While generally secure, traffic could be intercepted by parties with physical access to the link. IPsec traffic is always encrypted, but it travels over public networks where interception attempts are more common.
Reliability and stability: MPLS services include service-level agreements that emphasize uptime and consistent performance. IPsec depends on internet connectivity, which may experience congestion, packet loss, or route changes.
Quality of service (QoS): MPLS natively supports traffic prioritization, making it suitable for voice and latency-sensitive applications. IPsec can support QoS at the edge, but performance is ultimately constrained by the public internet.
MPLS vs. SD-WAN
MPLS and SD-WAN are both used to build wide area networks, but they are based on different architectural principles. MPLS relies on provider-managed private circuits, while SD-WAN uses software-based control to route traffic across multiple link types. The key differences are outlined below.
Traffic control and routing logic: SD-WAN uses centralized policies to steer application traffic dynamically across available links. Routing decisions adapt in real time based on performance and policy rules. MPLS uses predefined routing paths managed by the service provider.
Bandwidth utilization and scalability: SD-WAN can aggregate multiple connections, such as broadband, fiber, and MPLS, to maximize available bandwidth. Capacity can be increased by adding new links. MPLS scaling requires provisioning additional private circuits, which increases cost and deployment time.
Cloud and internet access: SD-WAN enables direct access from branch locations to cloud services and the internet. This reduces latency and avoids unnecessary traffic redirection. MPLS typically follows a hub-and-spoke model, where traffic is routed through a central data center before reaching external destinations.
Network backhauling: SD-WAN minimizes backhauling by creating optimized paths between branches, data centers, and cloud platforms. MPLS often backhauls traffic to central hubs, increasing delay and consuming reserved bandwidth.
Cost efficiency: SD-WAN lowers overall WAN cost by combining internet links with private connections and assigning traffic based on sensitivity. MPLS incurs higher costs due to dedicated infrastructure and performance guarantees.
Security approach: MPLS relies on private network isolation for security. SD-WAN secures traffic using encryption and secure tunnels across public networks.
MPLS FAQs
Is MPLS a LAN or WAN?
MPLS is a WAN technology. It is used to connect geographically distributed locations, such as branch offices and data centers, over long distances.
What is the difference between MPLS and VPN?
MPLS uses private, provider-managed network paths with predictable performance, while VPNs typically run over the public internet and rely on encryption for security rather than guaranteed routing paths.
What is MPLS for dummies?
MPLS is a way to send data across a network using fixed, predefined paths so traffic arrives faster and more reliably, especially between multiple business locations.
How does MPLS optimize network traffic?
MPLS optimizes traffic by directing data along predetermined paths, reducing routing decisions, minimizing congestion, and improving performance consistency for critical applications.
Multiprotocol Label Switching (MPLS) plays an important role in enterprise networking where performance, reliability, and traffic control matter. Through an introductory article by Axclusive on MPLS, the technology is presented as a strategic connectivity solution that enables predictable performance, optimized traffic flow, and stable communication for complex enterprise network environments.